


National Portrait Gallery hit by 350,000 email attacks in three months
The National Portrait Gallery was targeted by 347,602 emails containing spam, phishing and malware attacks in the last quarter of 2019, Freedom of Information (FOI) requests have been revealed. According to data collected by think tank Parliament Street, over half of the emails, 194,620 were identified as directory harvest attacks (DHA), used to harvest legitimate…
What is JavaScript? Complete Introduction with Hello World! Example Part 1
What is JavaScript? JavaScript is a very powerful client-side scripting language. JavaScript is primarily used to enhance user interaction with a webpage. In other words, you can make your webpage more lively and interactive with the help of JavaScript. JavaScript is also being widely used in game development and mobile application development. Javascript History JavaScript…

Dialing Back Business Email Compromise
Sophisticated cybercriminals continue to steal large sums of money from organizations of all sizes using business email compromise (BEC) schemes. Once the fraudulent payments are approved and transferred to the criminal’s accounts, they are very difficult to recover—and the targeted organization is liable for the resulting losses. Therefore, it’s vital to create a robust callback…

GDBFrontend – An Easy, Flexible And Extensionable GUI Debugger
GDBFrontend is an easy, flexible and extensionable gui debugger. Installing Deb Package (Debian / Ubuntu / KDE Neon) You can install GDBFrontend via deb package for Debian-based distributions. You can install it from following commands: echo “deb [trusted=yes] https://oguzhaneroglu.com/deb/ ./” | sudo tee -a /etc/apt/sources.list > /dev/null sudo apt update sudo apt install gdbfrontend After…
![[DeNA formula] Article mass production SEO method [I will explain in 5 steps] DeNA seo](https://www.itjd.in/wp-content/uploads/2021/11/DeNA-seo.jpg)
[DeNA formula] Article mass production SEO method [I will explain in 5 steps]
The Welq case is new to my memory, but there is a new move. Dena seo DeNA seems to have begun to consider a path to a resurgence in the digital media arena. Today, DeNA announced that it has signed a basic agreement with Shogakukan to consider the digital media business.DeNA signs basic agreement with Shogakukan…
![[Never fail] How to identify a good SEO company seo company](https://www.itjd.in/wp-content/uploads/2021/11/seo-company.jpg)
[Never fail] How to identify a good SEO company
For those who are looking for a good SEO company. In this article, I will introduce four recommended companies and points to distinguish good SEO companies. If you make a mistake in choosing an SEO company, you will end up throwing money away, so please consider carefully while referring to the article. There are two points…
Intermediate: Why you can’t study web marketing by reading a book
To you who are thinking, “I understand the basics of web marketing, but how should I study in the future?” Study with a book? Seminar? Or employment? Conclusions should be learned from the data (practice). No books, seminars or employment required. So this time, I’ll write how to learn web marketing from data. I live in…

Best Reverse Engineering Tools for 2020
If you are thinking of all the main tools used by a modern software, then you are in luck because this article is going for them. Therefore, if you are from someone who is familiar with network interaction principles, assembler language, and has some level of experience related to Windows programming using API functions, then…

Bob 1.0.1 – Hacking Challenge Walkthrough
The BOB 1.0.1 machine is available on VulnHub. It is intended for beginners/intermediates. Getting the initial shell was very easy although you may have to spend several hours finding the root. I would use Parrot Sec OS but you can use Kali Linux or any other Linux distro that you want. Open your terminal and…

Pureblood Tool – web Application Penetration Testing
Pureblood Information Gathering and Security Auditing Tool Pureblood is a Python tool that can be used during the information gathering and gaining access phases of penetration testing. Pureblood can collect useful information about target web applications, such as Banner grabbing, WHOIS record, DNS data, reverse DNS lookup, reverse IP lookup, CMS information, ports information, admin panel paths, subdomain scan…

PUBG Mobile India release date
The teaser did not reveal the PUBG Mobile India launch date but reiterated that the game is “coming soon”. This is a piece of important news for the lakhs of PUBG lovers in India. PUBG Mobile India’s official YouTube channel teased the launch of mobile games in India. However, shortly after uploading the PUBG…

Awesome Android Security – A Curated List Of Android Security Materials And Resources For Pentesters And Bug Hunters
A curated list of Android Security materials and resources For Pentesters and Bug Hunters. Blog AAPG – Android application penetration testing guide TikTok: three persistent arbitrary code executions and one theft of arbitrary files TikTok Persistent arbitrary code execution in Android’s Google Play Core Library: details, explanation and the PoC – CVE-2020-8913 Android: Access to…

What are the different roles within cybersecurity?
People talk about the cyber security job market, as if it is a monolith, but there are a variety of roles within cyber skills, which depends not only on your skill level and experience, but what you like to do. In fact, Cybercrime Magazine produced a list of 50 cyberspace job titles, while CyberSN, a…

Starting up xrdp in kali linux
So, I wanted to give someone access to my Kali linux box and this is what I did: Starting up xrdp in kali linux following steps root@kali1:~# apt-get install xrdp Reading package lists… Done Building dependency tree Reading state information… Done xrdp is already the newest version. The following packages were automatically installed and are no…
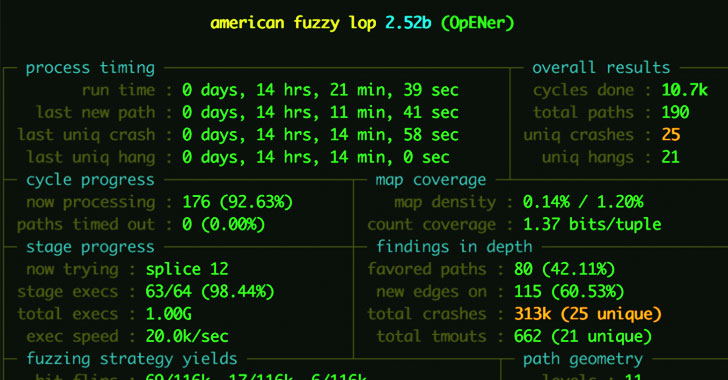
Severe Bugs Reported in EtherNet/IP Stack for Industrial Systems
The US Cyber Security and Infrastructure Security Agency (CISA) on Thursday issued an advisory warning of several vulnerabilities in the Opener EtherNet / IP stack, which could cause industrial systems to be denied service (DoS) attacks, data leaks, and remote code. Performance. All opener versions and versions prior to February 10, 2021 are affected, although…





